To prepare for cyberattack-induced grid outages, you should update your security protocols regularly, enforce strong passwords, and implement multi-factor authentication. Establish reliable emergency communications like satellite phones and drill response plans frequently. Develop and test an incident response strategy with local experts, and ensure critical data is backed up securely off-site. Investing in redundancies and staff training helps you stay resilient. Continue exploring more ways to strengthen your preparedness and safeguard critical infrastructure.
Key Takeaways
- Implement layered cybersecurity defenses and regular software updates to prevent breaches.
- Develop and routinely test incident response plans for quick containment and recovery.
- Establish alternative communication channels like satellite phones and radio systems for outages.
- Maintain secure backups and redundant power sources to ensure critical operations continue.
- Conduct staff training on cybersecurity awareness and crisis protocols to enhance preparedness.

As cyberattacks targeting power grids become increasingly sophisticated, it’s essential to prepare for potential outages before they happen. Power grids are complex, interconnected systems vulnerable to malicious actors seeking to disrupt critical services. To minimize damage and guarantee a swift response, you need to establish robust cybersecurity protocols. These protocols involve regular updates to software, strong password policies, multi-factor authentication, and continuous network monitoring. By implementing layered security measures, you reduce the risk of unauthorized access and detect threats early. Training staff on cybersecurity awareness is equally important, as human error often opens doors for cybercriminals. Educate your team on recognizing phishing attempts, suspicious activity, and the importance of following security best practices.
In addition to cybersecurity measures, having a well-planned emergency communication system is indispensable. In the event of a cyberattack, traditional communication channels like email or internet-based messaging might become compromised or unavailable. Prepare alternative methods such as radio systems, satellite phones, or pre-arranged emergency contacts. Clear, reliable communication ensures that you can coordinate responses quickly and keep all stakeholders informed. Establishing a chain of command and predefined procedures helps streamline decision-making during a crisis, reducing confusion and delays. Regular drills and simulated cyberattack scenarios can test your communication protocols, revealing weaknesses and allowing you to refine your approach. Incorporating layered security measures enhances overall resilience against cyber threats and improves detection capabilities.
You should also develop a thorough incident response plan tailored to cyber threats. This plan outlines specific steps to isolate affected systems, contain the attack, and restore normal operations. Having this plan in place before an attack occurs means you’ll respond swiftly and effectively, minimizing downtime. Part of your response strategy should include working closely with cybersecurity experts and local authorities, ensuring you’re aligned with best practices and legal requirements. Keep detailed records of all incidents, actions taken, and lessons learned to improve your defenses over time.
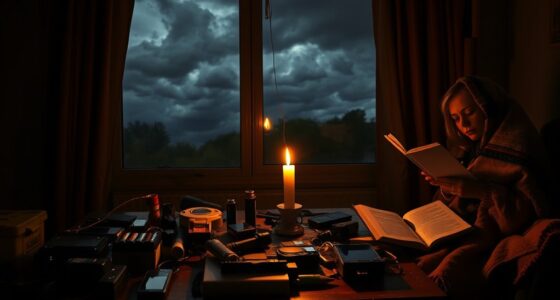
Furthermore, consider investing in backup systems and redundancies. Regularly backup critical data and store it securely off-site or in the cloud. These backups enable you to recover vital information quickly, reducing operational disruptions. You might also explore alternative power sources like generators or uninterruptible power supplies to maintain essential functions if the grid goes down. Being proactive and prepared helps you stay resilient in the face of evolving cyber threats. By combining strong cybersecurity protocols with effective emergency communication strategies, you’re better positioned to protect your infrastructure, guarantee safety, and restore normalcy swiftly after an attack.
Frequently Asked Questions
How Can Households Protect Their Personal Electronics During Outages?
You can safeguard your personal electronics during outages by keeping personal backups of important data on external drives or cloud storage. Additionally, assemble an emergency kit with portable chargers, batteries, and power banks to keep devices powered. Regularly update your backups and ensure your emergency kit is stocked and ready. This way, you’ll minimize data loss and stay connected even during a grid outage caused by a cyberattack.
What Legal Rights Do Consumers Have During a Grid Failure?
During a grid failure, you have legal recourse through consumer protections that safeguard your rights. Utilities must adhere to regulations, and if they fail, you can file complaints or seek compensation. Knowing your rights helps you hold providers accountable for outages caused by cyberattacks or other issues. Stay informed about local laws and utility policies, and don’t hesitate to pursue legal action if you experience neglect or unfair treatment during such disruptions.
How Often Should Critical Infrastructure Conduct Cyberattack Simulations?
You should conduct cyberattack drills at least annually to guarantee your critical infrastructure stays prepared. Regular cyberattack simulations help identify vulnerabilities and test response plans. Incorporate thorough risk assessments into your training to understand potential threats better. Frequent drills keep your team sharp, improve coordination, and ensure that everyone knows their roles during an actual cyber incident. Consistent practice is key to minimizing damage during a real cyberattack.
Are There International Standards for Grid Cybersecurity?
Yes, there are international standards for grid cybersecurity. You should follow international guidelines like the IEC 62443 series and NIST frameworks, which outline cybersecurity protocols to protect critical infrastructure. These standards help guarantee your systems are resilient against cyber threats and facilitate global cooperation. By adhering to these guidelines, you can strengthen your cybersecurity posture, reduce vulnerabilities, and respond effectively to potential cyberattacks on the power grid.
How Can Businesses Assess Their Vulnerability to Cyber-Induced Outages?
To assess your vulnerability to cyber-induced outages, start with a thorough risk assessment that identifies critical assets and potential threats. Conduct vulnerability scanning regularly to detect weaknesses in your systems. Review your cybersecurity protocols, employee training, and access controls. By continuously evaluating these areas, you can pinpoint gaps and strengthen defenses, reducing the likelihood of successful cyberattacks disrupting your operations. Stay proactive and adaptable in your approach.
Conclusion
While a cyberattack can threaten your power grid, preparation empowers you. You face the risk of sudden darkness, yet you can stay resilient by planning ahead. Stock supplies, secure your digital systems, and stay informed. In the shadow of potential outages, your readiness becomes a beacon of hope. Remember, the calm before the storm isn’t passive—it’s your chance to stand strong, turning vulnerability into strength and uncertainty into confidence.